Rochester System Security Lab
(GPU) System Security and Performance
We investigate practical security vulnerabilities in modern systems—particularly GPUs—and design performance-conscious defenses. Our research focuses on the following areas:
- GPU memory safety
- CPU/GPU side channels
- GPU microarchitectural optimization
Lab PI

Yanan Guo
Email: yanan.guo@rochester.edu
Website: yananguo.com
Assistant Professor
Department of Computer Science
University of Rochester
Research Highlights
GPU Side-Channel Attacks
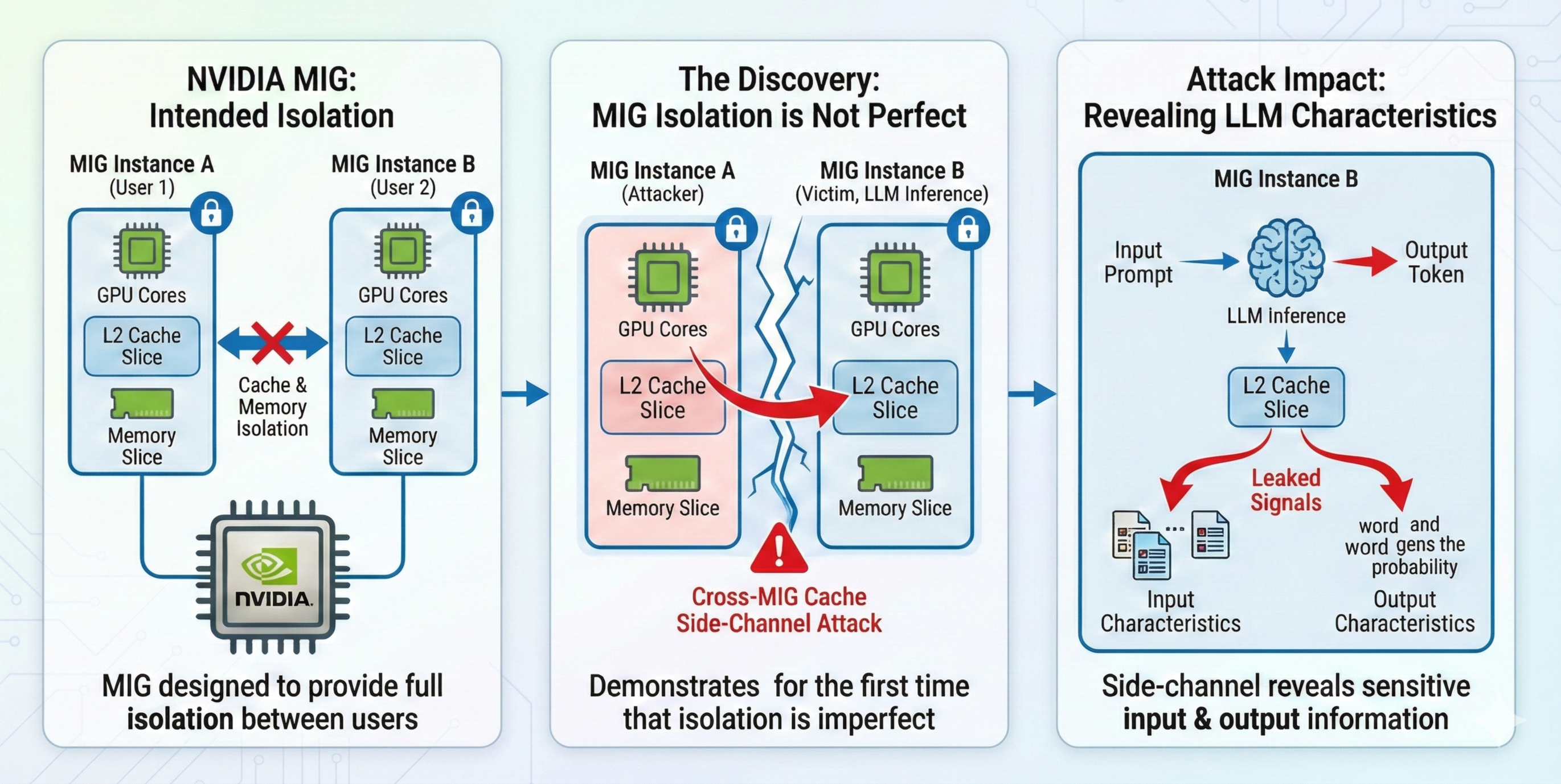
Side-Channel Attacks Across GPU Instances (USENIX Security'26)
- NVIDIA MIG is designed to provide cache and memory isolation between users.
- This work demonstrates, for the first time, that MIG’s isolation is not perfect.
- We introduce a cross-MIG cache side-channel attack that reveals input and output characteristics of LLM inference.
GPU Memory Safety
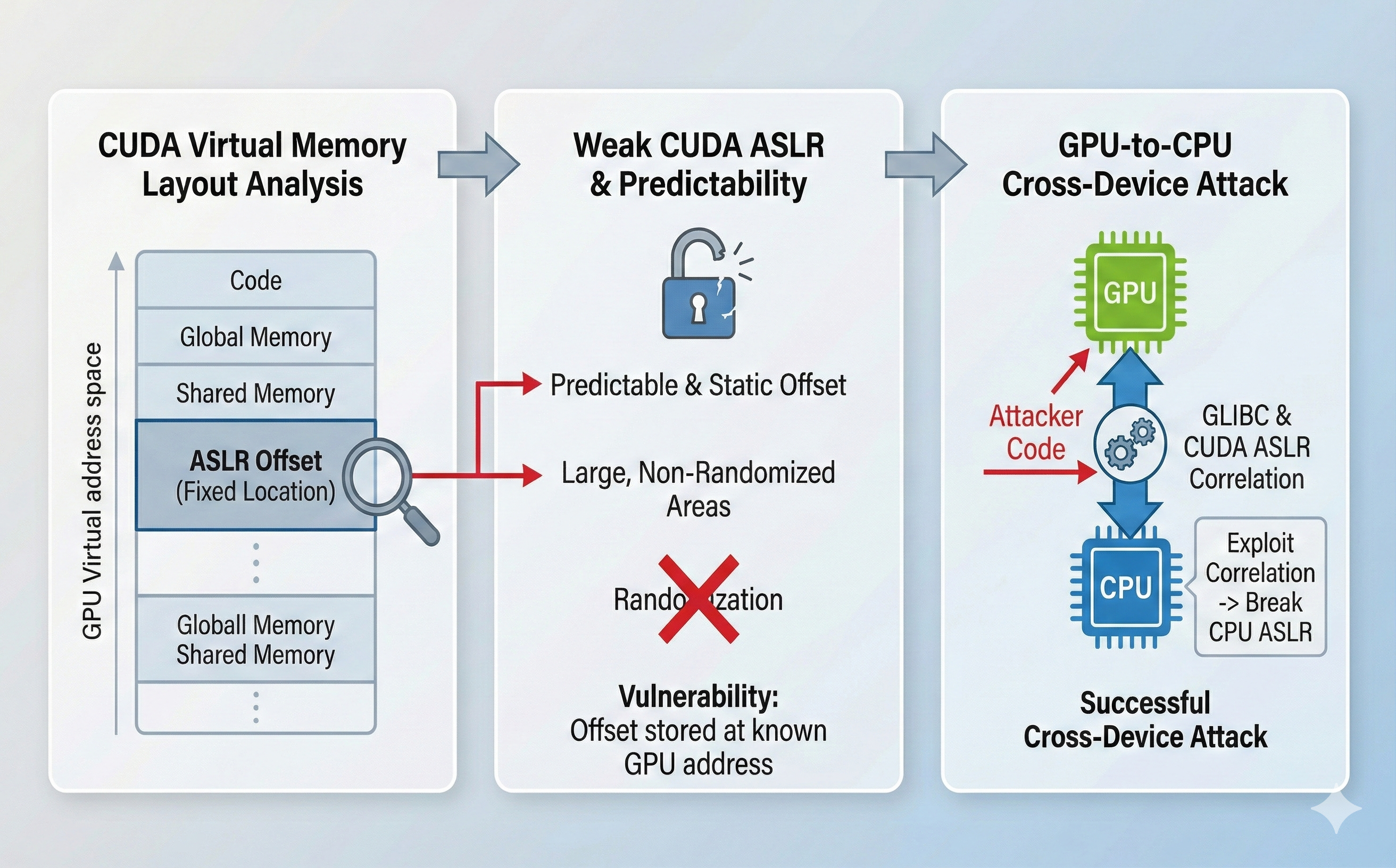
Attack on CUDA ASLR (IEEE S&P'26)
- This work conducts a thorough analysis of the virtual memory layout of CUDA programs.
- We identify several significant vulnerabilities in CUDA ASLR.
- One of the identified vulnerabilities enables a GPU-to-CPU attack.
- NVIDIA has fixed one of the identified vulnerabilities in driver version 570.
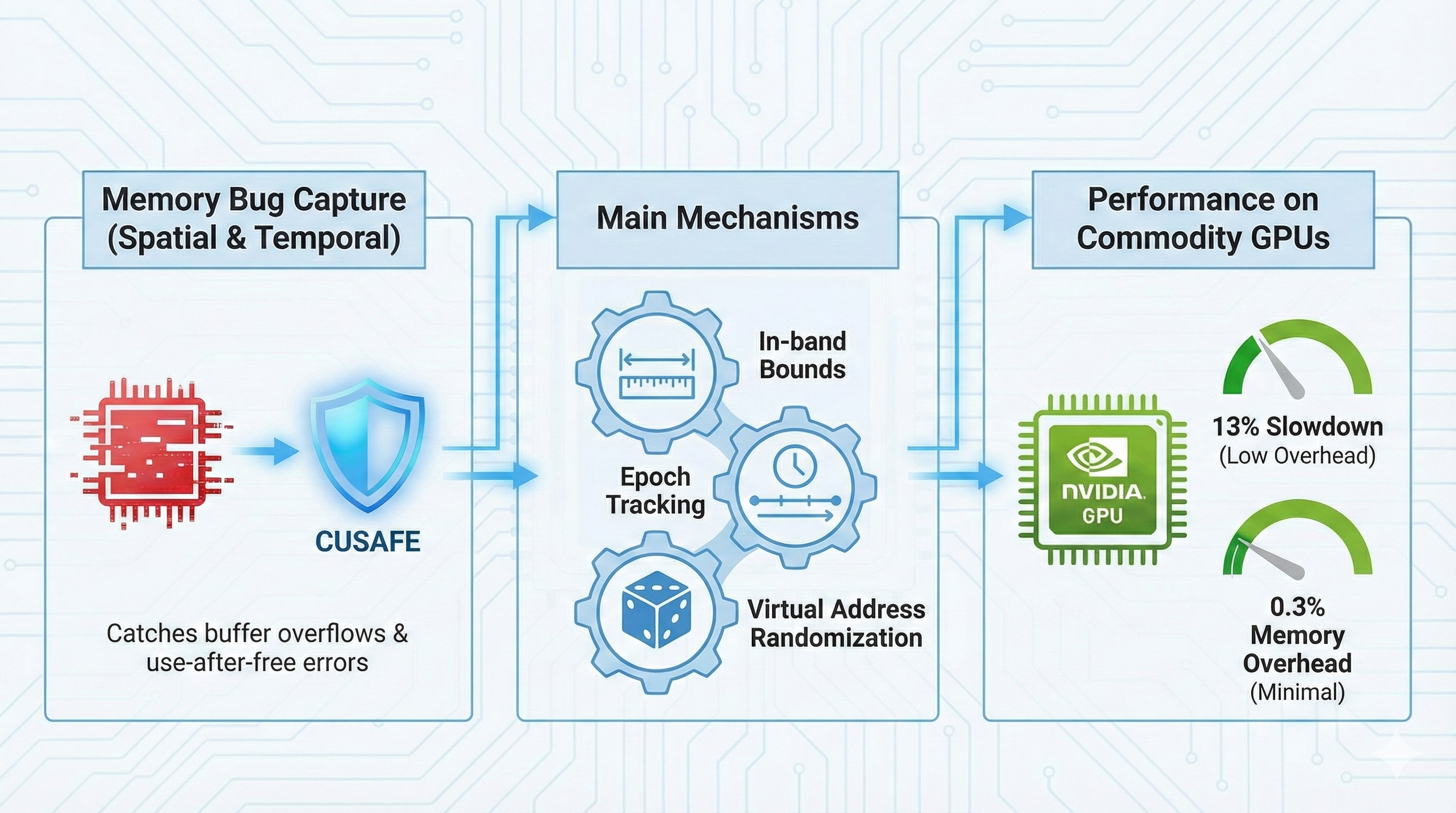
Memory Safety Tool for CUDA (USENIX Security'26)
- This work develops CuSafe, the first compiler-level framework for detecting spatial and temporal memory bugs in CUDA programs.
- Cusafe is open-source and runs on commodity NVIDIA GPUs without hardware or driver modifications.
- On average, CuSafe incurs 13% runtime slowdown and 0.3% memory overhead.
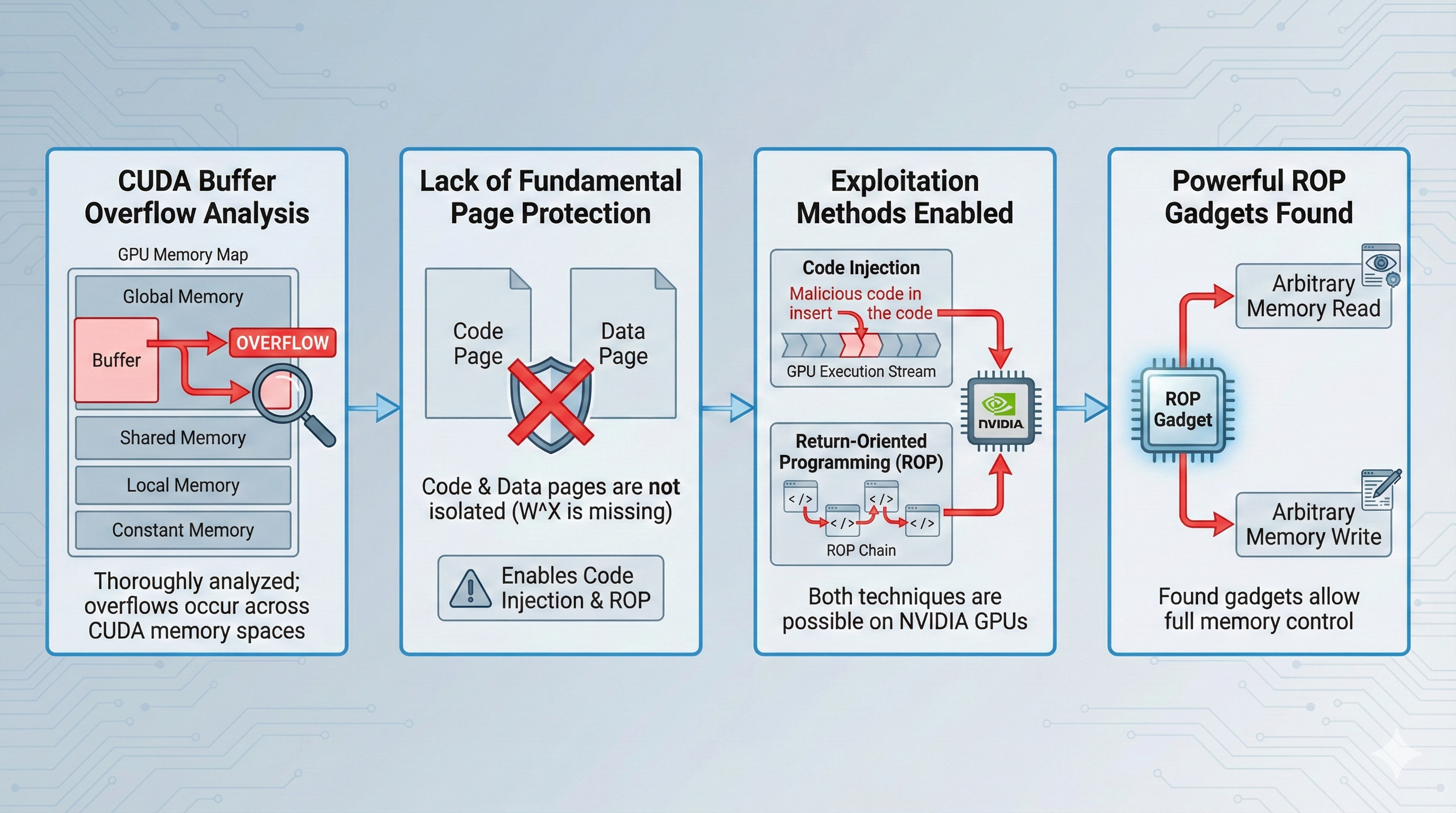
GPU Memory Exploitation (USENIX Security'24)
- This work thoroughly analyzes buffer overflow vulnerabilities in CUDA on NVIDIA GPUs.
- We show that buffer overflows can enable code injection and ROP attacks.
- We uncover powerful ROP gadgets in CUDA libraries, including arbitrary memory read/write primitives.
GPU Performance Characterization
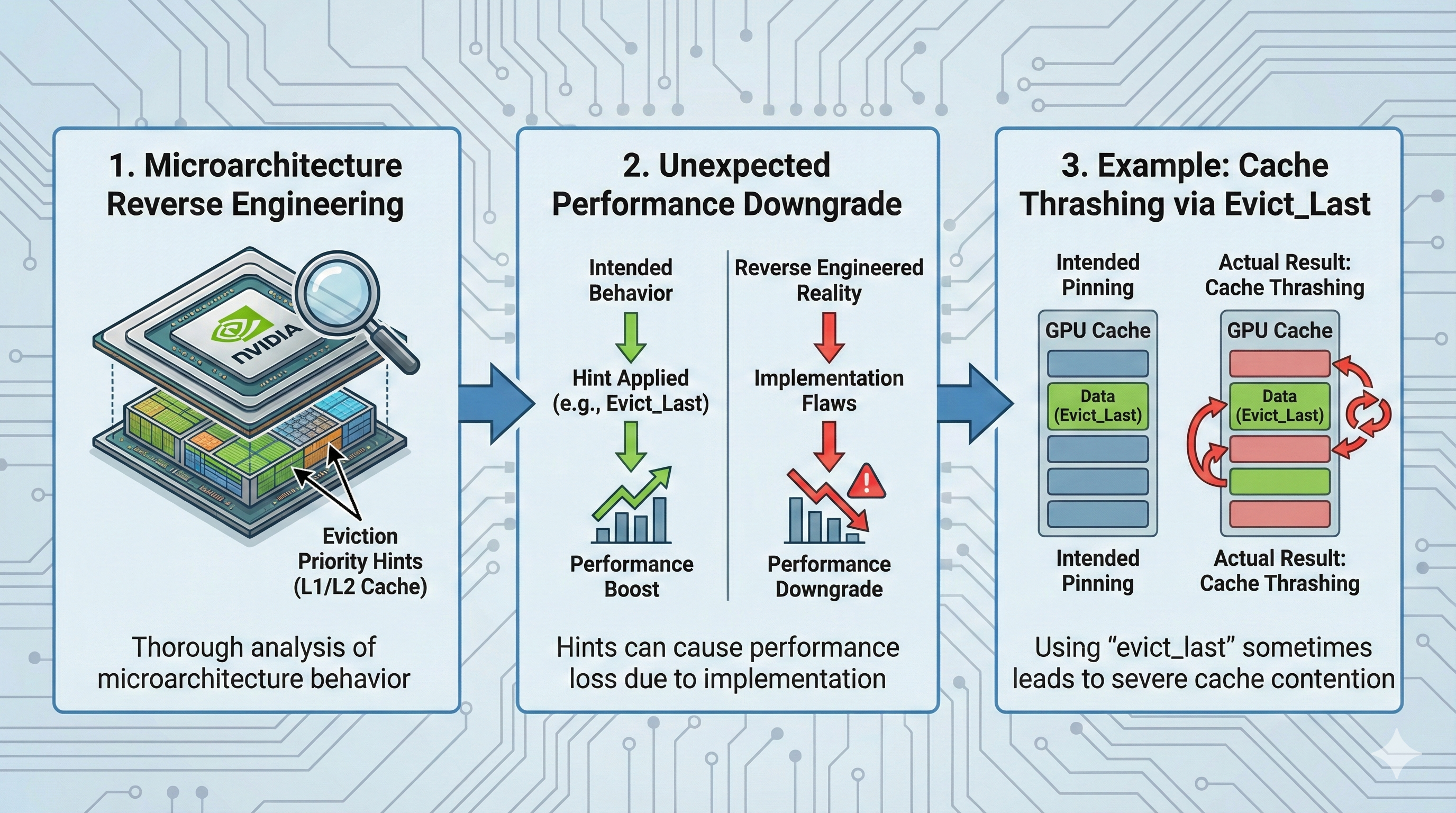
Characterization of Cache Eviction Priority Hints on NVIDIA GPUs (MICRO'25)
- This work reverse engineers the microarchitectural behavior of eviction priority hints on NVIDIA GPUs.
- We show that the current implementation of these hints can lead to unexpected performance degradation.
- For example, using evict_last to pin data in cache can instead trigger severe cache thrashing.